HAL TAMP Use Cases ¶
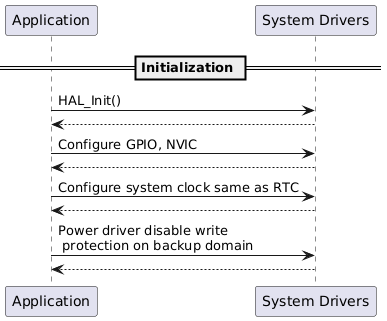
Initialization Sequence ¶
Passive Tamper Workflow ¶
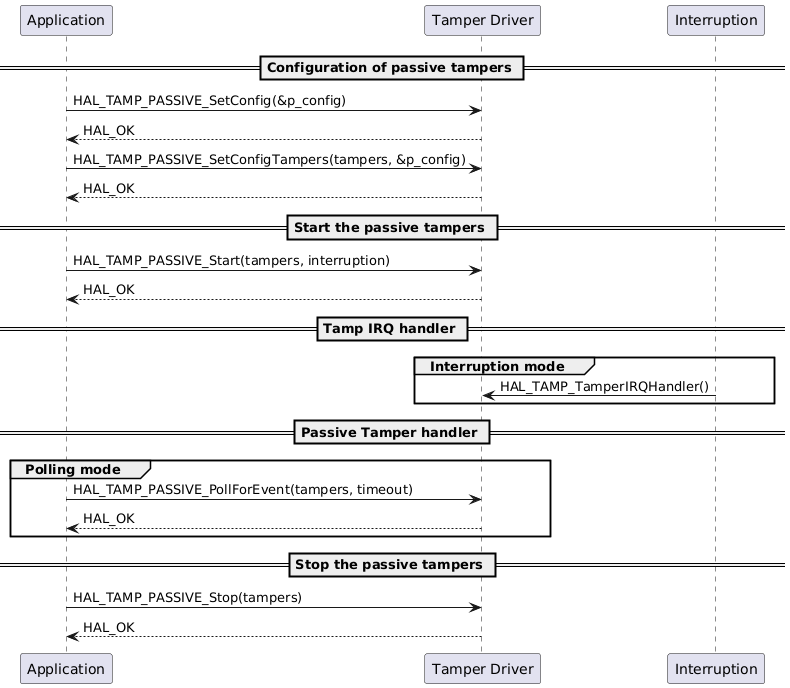
Functions called:
Internal Tamper Handling ¶
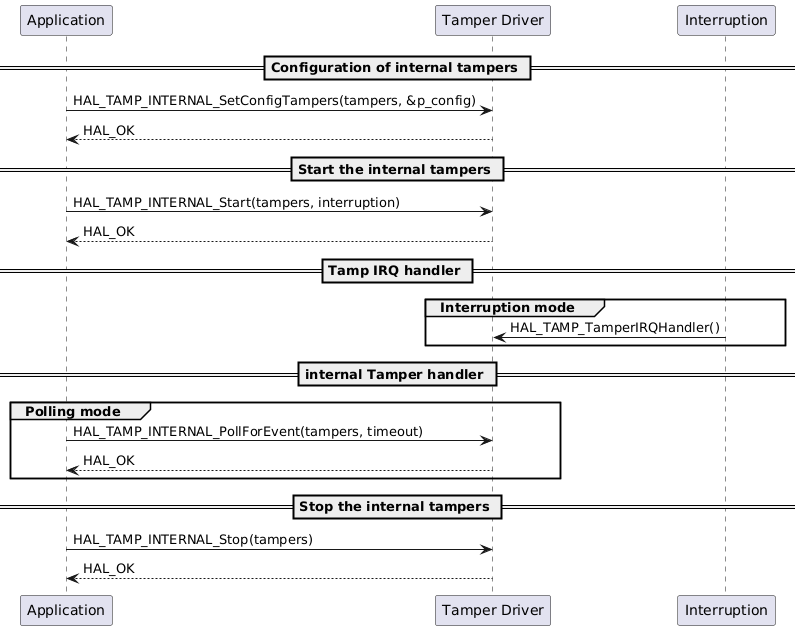
Functions called:
Backup Registers Usage Flow ¶
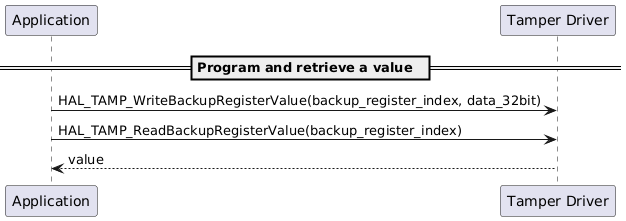
Functions called:
Device Secrets Management ¶
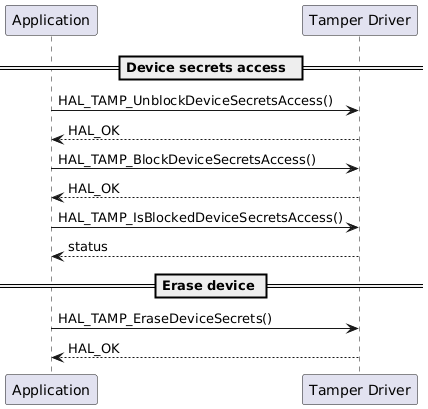
Functions called:
